In almost all assembly books you’ll find some nice tricks to do fast multiplications. E.g. instead of “imul eax, ebx, 3” you can do “lea eax, [ebx+ebx*2]” (ignoring flag effects). It’s pretty clear how this works. But how can we speed up, say, a division by 3? This is quite important since division is still a really slow operation. If you never thought or heart about this problem before, get pen and paper and try a little bit. It’s an interesting problem.
Transactor November 1987: Volume 8, Issue 3 (PDF)
The other day, I found this at WeirdStuff:
Create your own Version of Microsoft BASIC for 6502
Update: The source is available at github.com/mist64/msbasic
"ROR" in Microsoft BASIC for 6502
If you disassemble any version of Microsoft BASIC for 6502, you’ll find this code in a function that normalizes the (simulated) floating point accumulator:
Building the Solaris Kernel in 73 Easy Steps
Everyone and their grandmother builds Linux kernels. Many people build BSD, and some brave men even compile the OS X kernel every now and then. Why not compile your own Solaris kernel for a change?
Bill Gates' Personal Easter Eggs in 8 Bit BASIC
If you type “WAIT6502,1” into a Commodore PET with BASIC V2 (1979), it will show the string “MICROSOFT!” at the top left corner of the screen. Legend has it Bill Gates himself inserted this easter egg “after he had had an argument with Commodore founder Jack Tramiel”, “just in case Commodore ever tried to claim that the code wasn’t from Microsoft”.
The Xbox 360 Security System and its Weaknesses
After the disaster of the original Xbox, Microsoft put a lot of effort in designing what is probably the most sophisticated consumer hardware security system to date. We present its design, its implementation, its weaknesses, how it was hacked, and how to do it better next time.
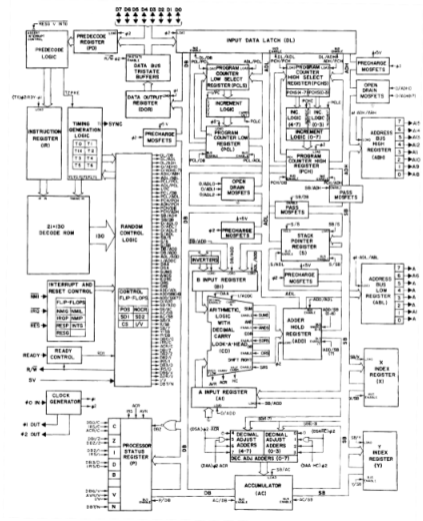
How MOS 6502 Illegal Opcodes really work
The original NMOS version of the MOS 6502, used in computers like the Commodore 64, the Apple II and the Nintendo Entertainment System (NES), is well-known for its illegal opcodes: Out of 256 possible opcodes, 151 are defined by the architecture, but many of the remaining 105 undefined opcodes do useful things.
Optimized Flags Code for 6502
When I disassembled Steve Wozniak’s Apple I BASIC, I found a 6502 trick that I had never seen before, although I had read a lot of 6502 code, including the very well-written Commodore BASIC (i.e. Microsoft BASIC for 6502).
1200 Baud Archeology: Reconstructing Apple I BASIC from a Cassette Tape
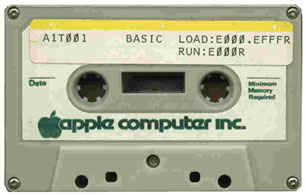
The audio file that was posted two weeks ago is indeed a very important artifact of computer history: It is a recording of the “Apple I BASIC” cassette tape that came with the Apple I. It is the first piece of Software ever sold by Apple (not counting computer firmware).
Puzzle: 1200 Baud Archeology
This audio file is an important (previously unreleased) artifact of computer history. The aim of the puzzle is to decode and identify it correctly.
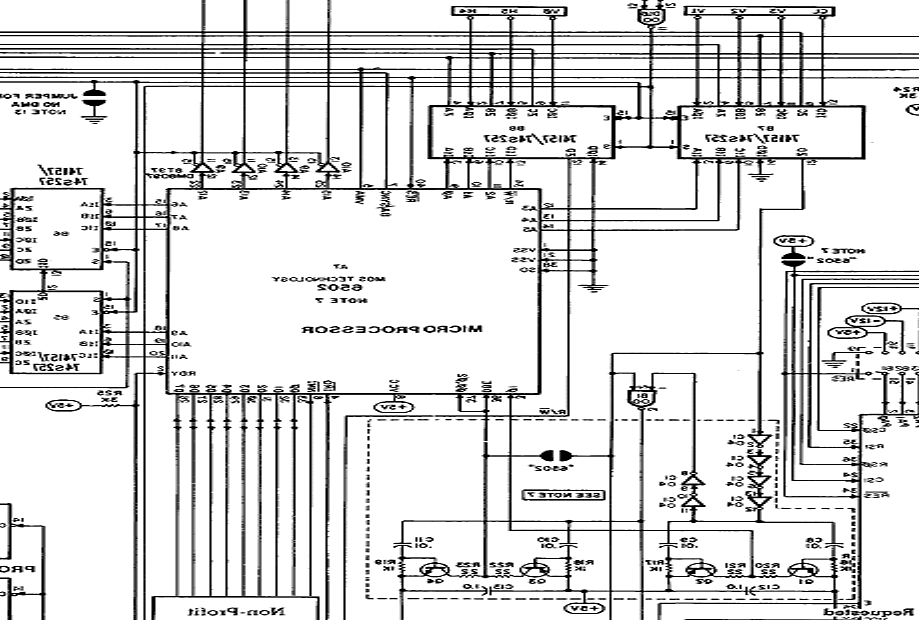
Tool's 'Rosetta Stoned' Live Performance to Include Apple I Schematic
It probably takes a geek in the front row (which is likely for a concert in San Francisco) to notice that the computer schematics Tool showed on the screens during their âRosetta Stonedâ performance are those of an Apple 1 – but distorted:
64 bit is a lot!
When people talk about porting their applications to 64 bit, I sometimes hear them wonder how long it will be until they have to port everything to 128 bit – after all, the swiches from 8 to 16 bit (e.g. CP/M to DOS), 16 to 32 bit (DOS/Windows 3 to Windows 95/NT) and 32 to 64 have all happened in the last 25 years.
Game Development Archeology: Zelda on Game Boy comes with source
Imagine you’re writing a Game Boy game, and the resulting ROM with all the code and data is just a little over one megabyte in size. No big deal, just pad the game to two megabytes, and use a 2 MB ROM in the cartridge. Just tell the linker to allocate 2 MB or RAM, put the actual data at the beginning, and then write a 2 MB “.gb” image to disk, which will then be sent to the ROM chip factory.
Switching modes with Style
pushl $(0xcb<<24)|0x08 call .-1
What does this instruction sequence do? (This was a collaborative effort by Chuck Gray, Myria and Michael.)
How retiring segmentation in AMD64 long mode broke VMware
UNIX, Windows NT, and all the operating systems in their class rely on virtual memory, or paging, in order to provide every process on the system a complete address space of its own. An easier way to protect processes from each other is segmentation: The 4 GB address space of a 32 bit CPU is divided into segments (consisting of a physical base address and a limit), one for each process, and every process may only access their own segment. This is what the 286 did.
Strange SSE3 opcodes
Intel used some strange opcodes for the SSE3 instructions. All MMX/SSE opcodes use the 0x0f prefix (former “pop cs”). They soon noticed the the 0x0f area gets full, so they used the 0x66, 0xf2, 0xf3 prefix as modifiers. The basic rule is:
Shift oddities
Most of the x86 instructions will automatically alter the flags depending on the result. Sometimes this is rather frustrating because you actually what to preserve the flags as long as possible, and sometimes you miss a “mov eax, ecx” which alters the flags. But at least it’s guaranteed that an instruction either sets the flags or it doesn’t touch them, independent of the actual operation… Or is it?